Threat actors are increasingly abusing n8n, a widely used open‑source and AI‑assisted workflow automation platform, to conduct stealthy phishing campaigns, distribute malware, and perform covert device reconnaissance. By leveraging n8n’s legitimate and trusted infrastructure, attackers are able to evade traditional security defenses, blend malicious activity into normal traffic, and maintain persistent access to victim environments.
This activity underscores a growing trend in which cybercriminals repurpose productivity and automation platforms originally designed to improve developer efficiency into flexible and scalable attack frameworks. Tools like n8n offer extensive integration capabilities, automation logic, and cloud connectivity, making them particularly attractive for abuse.
Abuse of n8n Webhooks for Phishing and Malware Delivery
Researchers from Cisco Talos discovered that attackers are exploiting n8n webhooks, which are URLs designed to trigger automated workflows, as a delivery mechanism for phishing lures and malware. These webhook URLs are embedded directly into phishing emails and act as the entry point for malicious workflows hosted on n8n infrastructure.
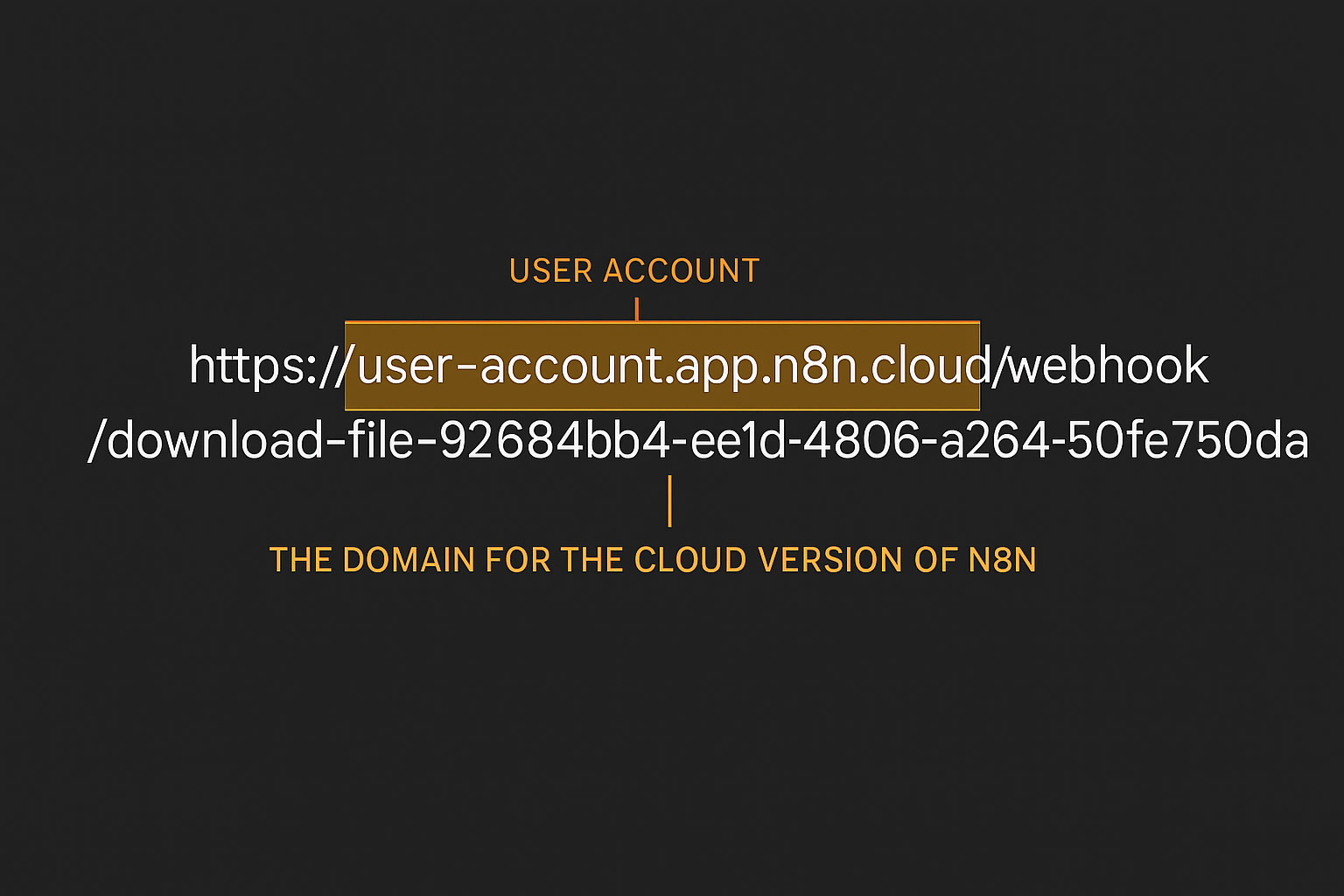
When a recipient clicks one of these links, the victim’s browser interacts with content that appears to originate from a trusted and reputable platform. Because the request is handled by n8n’s infrastructure, it often bypasses email security filters, URL reputation checks, and web gateways that rely on domain trust scoring.
Talos noted a marked increase in webhook abuse, driven by the ability to obscure the true origin of malicious payloads, dynamically customize content, and automate large‑scale campaigns with minimal effort.
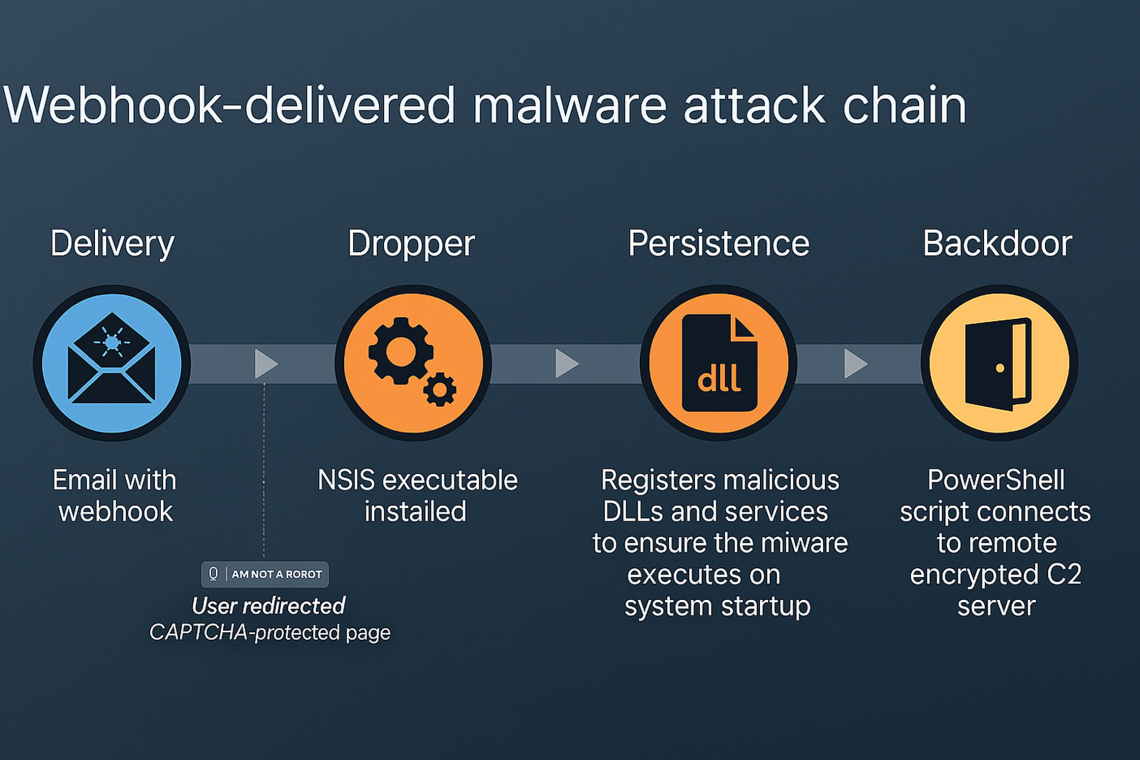
In one observed campaign, victims received phishing emails masquerading as Microsoft OneDrive sharing notifications. The embedded links redirected users to n8n‑hosted pages presenting a CAPTCHA challenge, a common tactic used to defeat automated analysis and lend legitimacy to the interaction. After the CAPTCHA was solved, users were prompted to download a file that appeared benign but ultimately delivered malware.
“Talos observed a phishing campaign that used an n8n‑hosted webhook link in emails purporting to be shared Microsoft OneDrive folders,” the report said. “Once the CAPTCHA is completed, a download button becomes visible, initiating a progress indicator as the payload is retrieved from an external host. Because the entire process is encapsulated within JavaScript executed in the browser, the download appears to originate from the n8n domain.”
This technique allows attackers to disguise malicious file delivery as trusted automation traffic, significantly reducing the likelihood of detection.
Malware Payloads and Persistent Access
In the campaign analyzed by Talos, the downloaded executable used PowerShell‑based commands to install Datto Remote Monitoring and Management (RMM) software on the victim system. The malware configured the tool as a scheduled task, ensuring persistence, established communication with a remote relay server, and then removed the original payload to minimize forensic evidence.
Talos also identified a separate but related campaign leveraging n8n webhooks to deliver a malicious MSI installer, again protected behind a CAPTCHA‑gated phishing page. This installer was disguised as a OneDrive document and deployed a modified version of the ITarian RMM tool.
Once installed, the altered RMM component functioned as a covert backdoor, allowing attackers to remotely control the system, exfiltrate sensitive data, and potentially deploy additional payloads. A decoy installer interface was used to distract users while malicious activity occurred in the background.
Device Fingerprinting and Reconnaissance
Beyond malware delivery, attackers have also abused n8n for device fingerprinting and victim validation. By embedding invisible tracking images often referred to as tracking pixels into phishing emails, attackers can exploit n8n webhooks to collect intelligence on targets.
When an email is opened, the hidden image triggers an HTTP request to an n8n webhook URL containing a unique identifier. This allows attackers to confirm that the email was accessed and gather metadata such as IP address, browser type, operating system, and approximate geographic location. This information can then be used to prioritize targets, tailor follow‑up attacks, or determine whether malware delivery is worthwhile.
The Broader Security Implications
Cisco Talos emphasized that the same automation capabilities that make tools like n8n valuable to developers such as low‑code workflow creation, seamless cloud integration, and event‑driven execution also make them highly adaptable for malicious purposes when abused.
“The workflows designed to save developers hours of manual effort are now being repurposed to automate malware delivery and large‑scale fingerprinting,” the report concluded. “Their flexibility, ease of integration, and ability to operate quietly make them ideal tools for attackers.”
As organizations increasingly adopt low‑code and AI‑driven automation platforms, security teams face the challenge of ensuring these tools remain assets rather than liabilities. The abuse of n8n highlights the need for stronger monitoring of trusted infrastructure, improved detection of malicious automation logic, and greater awareness of how legitimate platforms can be weaponized.
Defenders are urged to scrutinize outbound automation traffic, validate webhook usage, monitor for suspicious RMM deployments, and educate users about phishing techniques that leverage trusted brands and infrastructure. Without these safeguards, automation platforms risk becoming a critical blind spot in modern defensive strategies.
Found this article interesting? Follow us on X(Twitter) ,Threads and FaceBook to read more exclusive content we post.